jcasbinз®Җд»Ӣпјҡ
jcasbin жҳҜдёҖдёӘз”Ё Java иҜӯиЁҖжү“йҖ зҡ„иҪ»йҮҸзә§ејҖжәҗи®ҝй—®жҺ§еҲ¶жЎҶжһ¶https://github.com/casbin/jcasbinпјҢжҳҜcasbinзҡ„JavaиҜӯиЁҖзүҲжң¬гҖӮзӣ®еүҚеңЁ GitHub ејҖжәҗгҖӮjcasbin йҮҮз”ЁдәҶе…ғжЁЎеһӢзҡ„и®ҫи®ЎжҖқжғіпјҢж”ҜжҢҒеӨҡз§Қз»Ҹе…ёзҡ„и®ҝй—®жҺ§еҲ¶ж–№жЎҲпјҢеҰӮеҹәдәҺи§’иүІзҡ„и®ҝй—®жҺ§еҲ¶ RBACгҖҒеҹәдәҺеұһжҖ§зҡ„и®ҝй—®жҺ§еҲ¶ ABAC зӯүгҖӮ
jcasbin зҡ„дё»иҰҒзү№жҖ§еҢ…жӢ¬пјҡ
1.ж”ҜжҢҒиҮӘе®ҡд№үиҜ·жұӮзҡ„ж јејҸпјҢй»ҳи®Өзҡ„иҜ·жұӮж јејҸдёә{subject, object, action}пјӣ
2.е…·жңүи®ҝй—®жҺ§еҲ¶жЁЎеһӢ model е’Ңзӯ–з•Ҙ policy дёӨдёӘж ёеҝғжҰӮеҝөпјӣ
3.ж”ҜжҢҒ RBAC дёӯзҡ„еӨҡеұӮи§’иүІз»§жүҝпјҢдёҚжӯўдё»дҪ“еҸҜд»Ҙжңүи§’иүІпјҢиө„жәҗд№ҹеҸҜд»Ҙе…·жңүи§’иүІпјӣ
4.ж”ҜжҢҒи¶…зә§з”ЁжҲ·пјҢеҰӮ root жҲ– AdministratorпјҢи¶…зә§з”ЁжҲ·еҸҜд»ҘдёҚеҸ—жҺҲжқғзӯ–з•Ҙзҡ„зәҰжқҹи®ҝй—®д»»ж„Ҹиө„жәҗпјӣ
5.ж”ҜжҢҒеӨҡз§ҚеҶ…зҪ®зҡ„ж“ҚдҪңз¬ҰпјҢеҰӮ keyMatchпјҢж–№дҫҝеҜ№и·Ҝеҫ„ејҸзҡ„иө„жәҗиҝӣиЎҢз®ЎзҗҶпјҢеҰӮ /foo/bar еҸҜд»Ҙжҳ е°„еҲ° /foo*
jcasbin дёҚеҒҡзҡ„дәӢжғ…пјҡ
1.иә«д»Ҫи®ӨиҜҒ authentication пјҲеҚійӘҢиҜҒз”ЁжҲ·зҡ„з”ЁжҲ·еҗҚгҖҒеҜҶз ҒпјүпјҢjcasbin еҸӘиҙҹиҙЈи®ҝй—®жҺ§еҲ¶гҖӮеә”иҜҘжңүе…¶д»–дё“й—Ёзҡ„组件иҙҹиҙЈиә«д»Ҫи®ӨиҜҒпјҢ然еҗҺз”ұ jcasbin иҝӣиЎҢи®ҝй—®жҺ§еҲ¶пјҢдәҢиҖ…жҳҜзӣёдә’й…ҚеҗҲзҡ„е…ізі»пјӣ
2.з®ЎзҗҶз”ЁжҲ·еҲ—иЎЁжҲ–и§’иүІеҲ—иЎЁгҖӮjcasbin и®Өдёәз”ұйЎ№зӣ®иҮӘиә«жқҘз®ЎзҗҶз”ЁжҲ·гҖҒи§’иүІеҲ—иЎЁжӣҙдёәеҗҲйҖӮпјҢjcasbin еҒҮи®ҫжүҖжңүзӯ–з•Ҙе’ҢиҜ·жұӮдёӯеҮәзҺ°зҡ„з”ЁжҲ·гҖҒи§’иүІгҖҒиө„жәҗйғҪжҳҜеҗҲжі•жңүж•Ҳзҡ„гҖӮ
йЎ№зӣ®жһ¶жһ„пјҡ
еҹәдәҺspringboot+springcloud+nacosзҡ„з®ҖеҚ•еҲҶеёғејҸйЎ№зӣ®пјҢйЎ№зӣ®дәӨдә’йҮҮз”ЁopenFeignжЎҶжһ¶пјҢеҚ•зӢ¬жҸҗеҸ–еҮәжқҘжҲҗдёәдёҖдёӘзӢ¬з«Ӣзҡ„modelпјҡfeign
зҲ¶pomж–Ү件пјҡ
<properties>
<spring-cloud.version>Hoxton.SR9</spring-cloud.version>
<druid.version>1.2.4</druid.version>
<spring-boot.version>2.2.6.RELEASE</spring-boot.version>
<spring-cloud-alibaba.version>2.2.9.RELEASE</spring-cloud-alibaba.version>
<sql.version>8.0.29</sql.version>
<jwt.version>0.9.0</jwt.version>
<swagger2.version>2.9.2</swagger2.version>
<jcasbin.version>1.32.1</jcasbin.version>
<jdbc-adapter.version>2.3.3</jdbc-adapter.version>
</properties>
<dependencies>
<dependency>
<groupId>com.distribute</groupId>
<artifactId>commonUtil</artifactId>
<version>${version}</version>
</dependency>
<dependency>
<groupId>org.casbin</groupId>
<artifactId>jcasbin</artifactId>
<version>${jcasbin.version}</version>
</dependency>
<dependency>
<groupId>org.casbin</groupId>
<artifactId>jdbc-adapter</artifactId>
<version>${jdbc-adapter.version}</version>
</dependency>
<dependency>
<groupId>org.springframework.boot</groupId>
<artifactId>spring-boot-starter</artifactId>
</dependency>
<dependency>
<groupId>org.springframework.boot</groupId>
<artifactId>spring-boot-configuration-processor</artifactId>
<optional>true</optional>
</dependency>
<dependency>
<groupId>org.projectlombok</groupId>
<artifactId>lombok</artifactId>
<optional>true</optional>
</dependency>
</dependencies>
<dependencyManagement>
<dependencies>
<dependency>
<groupId>com.distribute</groupId>
<artifactId>feign</artifactId>
<version>${version}</version>
</dependency>
<!--йүҙжқғ-->
<dependency>
<groupId>io.jsonwebtoken</groupId>
<artifactId>jjwt</artifactId>
<version>${jwt.version}</version>
</dependency>
<dependency>
<groupId>mysql</groupId>
<artifactId>mysql-connector-java</artifactId>
<version>${sql.version}</version>
<scope>runtime</scope>
</dependency>
<!--druid-->
<dependency>
<groupId>com.alibaba</groupId>
<artifactId>druid-spring-boot-starter</artifactId>
<version>${druid.version}</version>
</dependency>
<dependency>
<groupId>org.springframework.cloud</groupId>
<artifactId>spring-cloud-dependencies</artifactId>
<version>${spring-cloud.version}</version>
<type>pom</type>
<scope>import</scope>
</dependency>
<dependency>
<groupId>org.springframework.boot</groupId>
<artifactId>spring-boot-dependencies</artifactId>
<version>${spring-boot.version}</version>
<type>pom</type>
<scope>import</scope>
</dependency>
<dependency>
<groupId>com.alibaba.cloud</groupId>
<artifactId>spring-cloud-alibaba-dependencies</artifactId>
<version>${spring-cloud-alibaba.version}</version>
<type>pom</type>
<scope>import</scope>
</dependency>
</dependencies>
</dependencyManagement>
</project>
gatewayйЎ№зӣ®пјҡ
pomж–Ү件пјҡ
<dependencies>
<dependency>
<groupId>com.distribute</groupId>
<artifactId>feign</artifactId>
</dependency>
<dependency>
<groupId>org.springframework.cloud</groupId>
<artifactId>spring-cloud-starter-gateway</artifactId>
</dependency>
<dependency>
<groupId>com.alibaba.cloud</groupId>
<artifactId>spring-cloud-starter-alibaba-nacos-discovery</artifactId>
</dependency>
<dependency>
<groupId>com.alibaba.cloud</groupId>
<artifactId>spring-cloud-starter-alibaba-nacos-config</artifactId>
</dependency>
</dependencies>gatewayзӣёе…іж ёеҝғд»Јз Ғпјҡ
жіЁеҶҢдёӯеҝғйҮҮз”ЁnacosпјҢе…ідәҺnacosзҡ„дҪҝз”ЁеҸҜд»ҘиҮӘиЎҢеӯҰд№ пјҢдёҚжҳҜжң¬ж–Үе…ій”®гҖӮ
зҪ‘е…ійҮҮз”ЁgatewayпјҢж ёеҝғе°ұжҳҜgatewayдёӯзҡ„иҝҮж»ӨеҷЁжҺҘеҸЈпјҡGlobalFilterпјҡ
@Slf4j @Component @Order(value = Integer.MIN_VALUE) public class AuthorityGlobalFilter implements GlobalFilter, Ordered { @Autowired private ConfigProperty configProperty; @Autowired private AdminUserInterfaceFeign adminUserInterfaceFeign; @Override public Mono<Void> filter(ServerWebExchange exchange, GatewayFilterChain chain) { //filterзҡ„еүҚзҪ®еӨ„зҗҶ ServerHttpRequest request = exchange.getRequest(); String path = request.getPath().pathWithinApplication().value(); InetSocketAddress remoteAddress = request.getRemoteAddress(); //3 иҺ·еҫ—иҜ·жұӮеӨҙ пјҢиҺ·еҫ—tokenеҖј HttpHeaders headers = request.getHeaders(); //еҲӨж–ӯзҷҪеҗҚеҚ•е’ҢжҳҜеҗҰжңүжқғйҷҗ if (validateWhiteList(path)) { return chain //继з»ӯи°ғз”Ёfilter .filter(exchange) //filterзҡ„еҗҺзҪ®еӨ„зҗҶ .then(Mono.fromRunnable(() -> { ServerHttpResponse response = exchange.getResponse(); HttpStatus statusCode = response.getStatusCode(); log.info("иҜ·жұӮи·Ҝеҫ„:{},иҝңзЁӢIPең°еқҖ:{},е“Қеә”з Ғ:{}", path, remoteAddress, statusCode); })); } else if(hasPower(request)){ return chain //继з»ӯи°ғз”Ёfilter .filter(exchange) //filterзҡ„еҗҺзҪ®еӨ„зҗҶ .then(Mono.fromRunnable(() -> { ServerHttpResponse response = exchange.getResponse(); HttpStatus statusCode = response.getStatusCode(); log.info("иҜ·жұӮи·Ҝеҫ„:{},иҝңзЁӢIPең°еқҖ:{},е“Қеә”з Ғ:{}", path, remoteAddress, statusCode); })); }else { return noPower(exchange); } } @Override public int getOrder() { return 0; } /** * еҲӨж–ӯжҳҜеҗҰжңүжқғйҷҗ */ private boolean hasPower( ServerHttpRequest request) { HttpHeaders headers = request.getHeaders(); List<String> authorizationList = headers.getOrEmpty("Authorization"); if(authorizationList.size()==0){ return false; }else{ try { Claims claims = JwtUtil.parseJWT(authorizationList.get(0)); //еҲӨж–ӯtokenжҳҜеҗҰиҝҮжңҹ Date expireTime = claims.getExpiration(); Date now = new Date(); if (now.after(expireTime)) { return false; } String userName = claims.getSubject(); String path = request.getPath().pathWithinApplication().value(); String method = request.getMethodValue(); Policy checkPower = new Policy(userName,path,method); CommonResult result = adminUserInterfaceFeign.checkPower(checkPower); return result.isSuccess() && (Boolean) result.getData(); }catch (Exception e){ return false; } } } /** * зҪ‘е…іжӢ’з»қпјҢиҝ”еӣһResult * * @param */ private Mono<Void> noPower(ServerWebExchange serverWebExchange) { // жқғйҷҗдёҚеӨҹжӢҰжҲӘ serverWebExchange.getResponse().setStatusCode(HttpStatus.UNAUTHORIZED); DataBuffer buffer = serverWebExchange.getResponse().bufferFactory().wrap(JSONUtil.toJsonStr(CommonResult.error(HttpStatusCode.UNAUTHORIZED)).getBytes(StandardCharsets.UTF_8)); ServerHttpResponse response = serverWebExchange.getResponse(); response.setStatusCode(HttpStatus.UNAUTHORIZED); //жҢҮе®ҡзј–з ҒпјҢеҗҰеҲҷеңЁжөҸи§ҲеҷЁдёӯдјҡдёӯж–Үд№ұз Ғ response.getHeaders().add("Content-Type", "application/json;charset=UTF-8"); return response.writeWith(Mono.just(buffer)); } public boolean validateWhiteList(String requestPath) { for (String whiteList : configProperty.getWhiteList()) { if (requestPath.contains(whiteList) || requestPath.matches(whiteList)) { return true; } } return false; } }
зҪ‘е…ідёӯйҰ–е…Ҳж ЎйӘҢжҳҜеҗҰеұһдәҺзҷҪеҗҚеҚ•пјҢзҷҪеҗҚеҚ•еҸҜд»ҘеҶҷеңЁapplication.ymlдёӯпјҢйҖҡиҝҮе®һдҪ“зұ»еҠ иҪҪпјҡ
application.ymlпјҡ
distribute: config: whiteList: - admin/login - admin/role/checkPower
ConfigPropertyпјҡ
@Component @ConfigurationProperties(prefix = "distribute.config") @Data public class ConfigProperty { List<String> whiteList; }
и®ҝй—®зҡ„иө„жәҗпјҲжҜ”еҰӮControllerи·Ҝеҫ„пјүеҰӮжһңдёҚеӯҳеңЁдәҺзҷҪеҗҚеҚ•пјҢеҲҷйҖҡиҝҮFeignи°ғз”Ёadmin-userйЎ№зӣ®дёӯзҡ„йүҙжқғж–№жі•иҝӣиЎҢйүҙжқғпјҢе…ідәҺadmin-userйЎ№зӣ®д»ҘеҸҠfeignзҡ„дҪҝз”ЁпјҢеңЁд№ӢеҗҺдјҡжҸҗеҲ°пјҢGlobalFilterдёӯж¶үеҸҠзҡ„jwtе·Ҙе…·зұ»пјҢж–Үжң«дјҡз»ҷеҮәгҖӮ
admin-userйЎ№зӣ®пјҡ
pomж–Ү件пјҡ
<dependencies>
<dependency>
<groupId>com.distribute</groupId>
<artifactId>feign</artifactId>
</dependency>
<!--ж•°жҚ®еә“й©ұеҠЁ-->
<dependency>
<groupId>mysql</groupId>
<artifactId>mysql-connector-java</artifactId>
</dependency>
<!--ж•°жҚ®еә“иҝһжҺҘжұ -->
<dependency>
<groupId>com.alibaba</groupId>
<artifactId>druid-spring-boot-starter</artifactId>
</dependency>
<!--jdbcиҝһжҺҘж•°жҚ®еә“-->
<dependency>
<groupId>org.springframework.boot</groupId>
<artifactId>spring-boot-starter-jdbc</artifactId>
</dependency>
<!--жңҚеҠЎжіЁеҶҢдёҺеҸ‘зҺ°-->
<dependency>
<groupId>com.alibaba.cloud</groupId>
<artifactId>spring-cloud-starter-alibaba-nacos-discovery</artifactId>
</dependency>
<dependency>
<groupId>com.alibaba.cloud</groupId>
<artifactId>spring-cloud-starter-alibaba-nacos-config</artifactId>
</dependency>
<!--web-->
<dependency>
<groupId>org.springframework.boot</groupId>
<artifactId>spring-boot-starter-web</artifactId>
</dependency>
</dependencies>зҷ»еҪ•жҺ§еҲ¶еҷЁпјҲжөӢиҜ•пјүпјҡ
/** * @author пјҡfengwenzhe * @date пјҡCreated in 2023/2/3 11:41 * ж–Ү件иҜҙжҳҺпјҡ </p> */ @RestController @RequestMapping("admin") public class LoginCtrl { @PostMapping("login") public CommonResult login(@RequestBody Account account){ String token = JwtUtil.createJWT(UUID.randomUUID().toString(), account.getUserName(), 3600L*1000); Map<String,Object> result = new HashMap<>(); result.put("username",account.getUserName()); result.put("token",token); return CommonResult.ok(result); } }
jcasbinзҡ„ж•ҙеҗҲпјҡ
jcasbinеҸҜд»Ҙд»Һж–Ү件еҠ иҪҪи§’иүІжқғйҷҗдҝЎжҒҜпјҢжӯӨеӨ„е·Іж•ҙеҗҲжҲҗд»Һж•°жҚ®еә“еҠ иҪҪи§’иүІжқғйҷҗдҝЎжҒҜпјҢдёәжӯӨпјҢйңҖиҰҒдёәjcasbinй…ҚзҪ®ж•°жҚ®жәҗпјҲдёәдәҶж–№дҫҝзӣҙжҺҘдҪҝз”ЁйЎ№зӣ®дёӯзҡ„ж•°жҚ®еә“пјҢе®һйҷ…з”ҹдә§зҺҜеўғеҸҜд»ҘеҲҶејҖпјүд»ҘеҸҠжЁЎеһӢж–Ү件и·Ҝеҫ„пјҡ
application.ymlпјҡ
org: jcasbin: model-path: jcasbin/basic_model.conf spring: datasource: url: jdbc:mysql://localhost:3306/jcasbin?useSSL=false driver-class-name: com.mysql.jdbc.Driver username: root password: root
дҪҝз”ЁjcasbinйҰ–е…ҲйңҖиҰҒй…ҚзҪ®jcasbinе·ҘеҺӮзұ»пјҢеҲқе§ӢеҢ–enforcerпјҡ
@Component public class EnforcerFactory implements InitializingBean { private static Enforcer enforcer; @Autowired private EnforcerConfigProperties enforcerConfigProperties; @Autowired private DataSource dataSource; @Override public void afterPropertiesSet() throws Exception { //д»Һж•°жҚ®еә“иҜ»еҸ–зӯ–з•Ҙ JDBCAdapter jdbcAdapter = new JDBCAdapter(dataSource); String path = this.getClass().getClassLoader().getResource("").getPath(); enforcer = new Enforcer(path+enforcerConfigProperties.getModelPath(), jdbcAdapter); enforcer.loadPolicy();//Load the policy from DB. }
public static Enforcer getEnforcer(){ return enforcer; } }
@Configuration @ConfigurationProperties(prefix = "org.jcasbin") @Data public class EnforcerConfigProperties { private String modelPath; }
жӯӨеҗҺжүҖжңүеҜ№jcasbinзҡ„ж“ҚдҪңйғҪеҹәдәҺе®һдҫӢenforcerпјҢжӯӨж—¶е°ұеҸҜд»ҘиҝӣиЎҢдёҡеҠЎдёҠзҡ„ж–°еўһжқғйҷҗгҖҒи§’иүІгҖҒйүҙжқғзӯүзҡ„ејҖеҸ‘дәҶгҖӮ
RoleControllerи§’иүІжҺ§еҲ¶еҷЁпјҡ
package com.distribute.admin.ctrl; import com.distribute.admin.service.EnforcerFactory; import com.distribute.common.CommonResult; import com.distribute.entity.PermissionEntity; import com.distribute.entity.Policy; import org.springframework.web.bind.annotation.PostMapping; import org.springframework.web.bind.annotation.RequestBody; import org.springframework.web.bind.annotation.RequestMapping; import org.springframework.web.bind.annotation.RestController; /** * @author пјҡfengwenzhe * @date пјҡCreated in 2023/2/3 11:41 * ж–Ү件иҜҙжҳҺпјҡ </p> */ @RestController @RequestMapping("admin/role") public class RoleCtrl { /** *@Description <иҺ·еҸ–е…ЁйғЁи§’иүІ> *@return com.distribute.common.CommonResult *@date 2023/2/6 11:13 *@auther fengwenzhee */ @PostMapping("findAllRoleList") public CommonResult findAllRoleList(){ return EnforcerFactory.findAllRoleList(); } /** *@Description <жү№йҮҸж–°еўһ з”ЁжҲ·/и§’иүІ зҡ„жқғйҷҗ> *@param permissionEntity *@return com.distribute.common.CommonResult *@date 2023/2/6 11:13 *@auther fengwenzhee */ @PostMapping("batchAddPermission") public CommonResult batchAddPermission(@RequestBody PermissionEntity permissionEntity){ return EnforcerFactory.batchAddPermission(permissionEntity); } /** *@Description <жү№йҮҸеҲ йҷӨ з”ЁжҲ·/и§’иүІ зҡ„жқғйҷҗ> *@param permissionEntity *@return com.distribute.common.CommonResult *@date 2023/2/5 17:08 *@auther fengwenzhee */ @PostMapping("batchDeletePermission") public CommonResult batchDeletePermission(@RequestBody PermissionEntity permissionEntity){ return EnforcerFactory.batchDeletePermission(permissionEntity); } /** *@Description <жү№йҮҸдёәз”ЁжҲ·ж·»еҠ и§’иүІ> *@param permissionEntity *@return com.distribute.common.CommonResult *@date 2023/2/6 11:17 *@auther fengwenzhee */ @PostMapping("batchAddRoleForUser") public CommonResult batchAddRoleForUser(@RequestBody PermissionEntity permissionEntity){ return EnforcerFactory.batchAddRoleForUser(permissionEntity); } /** *@Description <жү№йҮҸеҲ йҷӨз”ЁжҲ·и§’иүІ> *@param permissionEntity *@return com.distribute.common.CommonResult *@date 2023/2/5 17:08 *@auther fengwenzhee */ @PostMapping("batchDeleteRoleForUser") public CommonResult batchDeleteRoleForUser(@RequestBody PermissionEntity permissionEntity){ return EnforcerFactory.batchDeleteRoleForUser(permissionEntity); } /** *@Description <жү№йҮҸеҲ йҷӨи§’иүІеҸҠе…¶ж¶үеҸҠеҲ°зҡ„з”ЁжҲ·дёҺи§’иүІе…ізі»> *@param permissionEntity *@return com.distribute.common.CommonResult *@date 2023/2/5 17:08 *@auther fengwenzhee */ @PostMapping("batchDeleteRole") public CommonResult batchDeleteRole(@RequestBody PermissionEntity permissionEntity){ return EnforcerFactory.batchDeleteRole(permissionEntity); } @PostMapping("checkPower") public CommonResult checkPower(@RequestBody Policy policy){ if(policy.getSub().equals("admin")){ //и¶…зә§з®ЎзҗҶе‘ҳзӣҙжҺҘж”ҫиЎҢ return CommonResult.ok(true); } String path = this.getClass().getClassLoader().getResource("").getPath(); // Enforcer enforcer = new Enforcer(path+"/jcasbin/basic_model.conf", path+"/jcasbin/basic_policy.csv"); д»Һжң¬ең°ж–Ү件еҠ иҪҪжқғйҷҗдҝЎжҒҜ if (EnforcerFactory.getEnforcer().enforce("user_"+policy.getSub(), policy.getObj(), policy.getAct())) { // permit alice to read data1 return CommonResult.ok(true); } else { // deny the request, show an error return CommonResult.ok(false); } } }
еҹәдәҺRBACзҡ„жЁЎеһӢж–Ү件basic_model.confпјҡ
[request_definition] r = sub, obj, act [policy_definition] p = sub, obj, act [role_definition] g = _, _ [policy_effect] e = some(where (p.eft == allow)) [matchers] m = g(r.sub, p.sub) && r.obj == p.obj && r.act == p.act
еңЁRoleControllerи§’иүІжҺ§еҲ¶еҷЁдёӯе·Із»ҸеҶҷеҘҪдәҶдёҖдәӣж–№жі•пјҢеҗҺз»ӯеҸҜд»Ҙж №жҚ®йңҖиҰҒиҮӘиЎҢж–°еўһпјҢе…ҘеҸӮе®һдҪ“жҲ‘з®ҖеҚ•е°ҒиЈ…дәҶдёҖдёӢпјҢ然еҗҺеҫӘзҺҜиҝӣиЎҢжү№йҮҸж“ҚдҪңпјҡ
PermissionEntity:
@Data public class PermissionEntity implements Serializable { private Integer type; //ж“ҚдҪңеҜ№иұЎжҳҜз”ЁжҲ·иҝҳжҳҜи§’иүІ private List<Policy> policyList; }
Policy:
@Data public class Policy implements Serializable { /**жғіиҰҒи®ҝй—®иө„жәҗзҡ„з”ЁжҲ· жҲ–иҖ…и§’иүІ*/ private String sub; /**е°ҶиҰҒи®ҝй—®зҡ„иө„жәҗпјҢеҸҜд»ҘдҪҝз”Ё * дҪңдёәйҖҡй…Қз¬ҰпјҢдҫӢеҰӮ/user/* */ private String obj; /**з”ЁжҲ·еҜ№иө„жәҗжү§иЎҢзҡ„ж“ҚдҪңгҖӮHTTPж–№жі•пјҢGETгҖҒPOSTгҖҒPUTгҖҒDELETEзӯүпјҢеҸҜд»ҘдҪҝз”Ё * дҪңдёәйҖҡй…Қз¬Ұ*/ private String act; /** * * @param sub жғіиҰҒи®ҝй—®иө„жәҗзҡ„з”ЁжҲ· жҲ–иҖ…и§’иүІ * @param obj е°ҶиҰҒи®ҝй—®зҡ„иө„жәҗпјҢеҸҜд»ҘдҪҝз”Ё * дҪңдёәйҖҡй…Қз¬ҰпјҢдҫӢеҰӮ/user/* * @param act з”ЁжҲ·еҜ№иө„жәҗжү§иЎҢзҡ„ж“ҚдҪңгҖӮHTTPж–№жі•пјҢGETгҖҒPOSTгҖҒPUTгҖҒDELETEзӯүпјҢеҸҜд»ҘдҪҝз”Ё * дҪңдёәйҖҡй…Қз¬Ұ */ public Policy(String sub, String obj, String act) { super(); this.sub = sub; this.obj = obj; this.act = act; } @Override public String toString() { return "Policy [sub=" + sub + ", obj=" + obj + ", act=" + act + "]"; } }
еңЁEnforcerFactoryдёӯж–°еўһRoleControllerеҜ№еә”ж–№жі•пјҡ
public static CommonResult batchAddPermission(PermissionEntity permissionEntity) { if(permissionEntity.getType()==null){ return CommonResult.error(HttpStatusCode.OPERATION_TYPE_REQUIRED); } if(permissionEntity.getType()==1){ //ж“ҚдҪңеҜ№иұЎдёәз”ЁжҲ· for (Policy policy:permissionEntity.getPolicyList()){ enforcer.addPermissionForUser("user_"+policy.getSub(),policy.getObj(),policy.getAct()); } }else if(permissionEntity.getType()==2){ //ж“ҚдҪңеҜ№иұЎдёәи§’иүІ for (Policy policy:permissionEntity.getPolicyList()){ enforcer.addPermissionForUser("role_"+policy.getSub(),policy.getObj(),policy.getAct()); } }else { return CommonResult.error(HttpStatusCode.OPERATION_TYPE_ERROR); } return CommonResult.ok(true); } public static CommonResult batchAddRoleForUser(PermissionEntity permissionEntity) { for (Policy policy:permissionEntity.getPolicyList()){ enforcer.addRoleForUser("user_"+policy.getSub(),"role_"+policy.getObj()); } return CommonResult.ok(true); } public static CommonResult batchDeleteRole(PermissionEntity permissionEntity) { for (Policy policy:permissionEntity.getPolicyList()){ enforcer.deleteRole("role_"+policy.getSub()); } return CommonResult.ok(true); } public static CommonResult batchDeleteRoleForUser(PermissionEntity permissionEntity) { for (Policy policy:permissionEntity.getPolicyList()){ enforcer.deleteRoleForUser("user_"+policy.getSub(),"role_"+policy.getObj()); } return CommonResult.ok(true); } public static CommonResult batchDeletePermission(PermissionEntity permissionEntity) { if(permissionEntity.getType()==null){ return CommonResult.error(HttpStatusCode.OPERATION_TYPE_REQUIRED); } if(permissionEntity.getType()==1){ //ж“ҚдҪңеҜ№иұЎдёәз”ЁжҲ· for (Policy policy:permissionEntity.getPolicyList()){ enforcer.deletePermissionForUser("user_"+policy.getSub(),policy.getObj(),policy.getAct()); } }else if(permissionEntity.getType()==2){ //ж“ҚдҪңеҜ№иұЎдёәи§’иүІ for (Policy policy:permissionEntity.getPolicyList()){ enforcer.deletePermissionForUser("role_"+policy.getSub(),policy.getObj(),policy.getAct()); } }else { return CommonResult.error(HttpStatusCode.OPERATION_TYPE_ERROR); } return CommonResult.ok(true); } public static CommonResult findAllRoleList() { List<String> roles = new ArrayList<>(); for (String role:enforcer.getAllRoles()){ roles.add(role.split("role_")[1]); } return CommonResult.ok(roles); }
PS:jcasbinдёӯеҜ№жқғйҷҗзҡ„жҠҠжҺ§жҳҜеҹәдәҺsubjectзҡ„пјҢжүҖд»Ҙж— жі•еҢәеҲҶжқғйҷҗжҳҜз”ЁжҲ·иҝҳжҳҜи§’иүІзҡ„пјҢеңЁиҝҷйҮҢз”ЁеүҚзјҖжҳҜuser_иҝҳжҳҜrole_жқҘеҢәеҲҶпјҢж•°жҚ®еә“жөӢиҜ•ж•°жҚ®еҰӮдёӢпјҡ
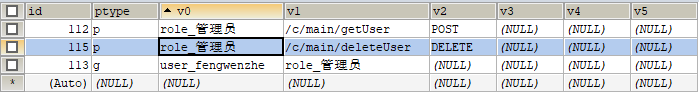
ж„ҸжҖқжҳҜrole_з®ЎзҗҶе‘ҳи§’иүІдёӢжңүдёӨдёӘжқғйҷҗпјҢеҲҶеҲ«жҳҜ/c/main/getUser POSTпјҢе’Ң/c/main/deleteUser DELETEпјҢv1еӯ—ж®өеҸҜд»Ҙи§Ҷдёәиө„жәҗпјҢv2дёәиҜ·жұӮеҠЁдҪңпјҢ
user_fengwenzheз”ЁжҲ·е…·жңүrole_з®ЎзҗҶе‘ҳзҡ„и§’иүІпјҢйүҙжқғж—¶еҸҜд»ҘеҰӮдёӢиҝӣиЎҢпјҡ
String path = request.getPath().pathWithinApplication().value(); String method = request.getMethodValue(); Policy checkPower = new Policy(userName,path,method); CommonResult result = adminUserInterfaceFeign.checkPower(checkPower);
жҜ”еҰӮжӯӨж—¶жҲ‘дј е…ҘuserName=fengwenzheпјҢpath=/c/main/getUser method=POSTпјҢе°ұеҸҜд»ҘйүҙжқғжҲҗеҠҹпјҢеӣ дёәжңүеүҚзјҖеӯҳеңЁпјҢд»Јз ҒдёӯиҮӘиЎҢиЎҘи¶і'user_'пјҡ
if (EnforcerFactory.getEnforcer().enforce("user_"+policy.getSub(), policy.getObj(), policy.getAct())) { // permit to read data return CommonResult.ok(true); } else { // deny the request, show an error return CommonResult.ok(false); }
feignйЎ№зӣ®пјҡ
еҸӘе®ҡд№үfeignзӣёе…іжҺҘеҸЈдёҺе®һзҺ°зұ»пјҡ
/** * @author пјҡfengwenzhe * @date пјҡCreated in 2023/2/2 21:48 * ж–Ү件иҜҙжҳҺпјҡ </p> */ @FeignClient(value = "platform-admin-user",fallback = AdminUserFeignImpl.class) @Component public interface AdminUserInterfaceFeign {
@PostMapping("admin/role/checkPower")
CommonResult checkPower(@RequestBody Policy policy);
/** *@Description <жү№йҮҸж–°еўһ з”ЁжҲ·/и§’иүІ зҡ„жқғйҷҗ> *@param permissionEntity *@return com.distribute.common.CommonResult *@date 2023/2/6 11:13 *@auther fengwenzhee */ @PostMapping("batchAddPermission") CommonResult batchAddPermission(@RequestBody PermissionEntity permissionEntity); }
package com.distribute.impl; import com.distribute.AdminUserInterfaceFeign; import com.distribute.common.CommonResult; import com.distribute.common.HttpStatusCode; import com.distribute.entity.PermissionEntity; import com.distribute.entity.Policy; import org.springframework.stereotype.Component; import org.springframework.web.bind.annotation.RequestBody; /** * @author пјҡfengwenzhe * @date пјҡCreated in 2023/2/2 22:03 * ж–Ү件иҜҙжҳҺпјҡ </p> */ @Component public class AdminUserFeignImpl implements AdminUserInterfaceFeign { @Override public CommonResult checkPower(@RequestBody Policy power) { return CommonResult.error(HttpStatusCode.REQUEST_TIMEOUT); } @Override public CommonResult batchAddPermission(PermissionEntity permissionEntity) { return CommonResult.error(HttpStatusCode.REQUEST_TIMEOUT); } }
gatewayеҗҜеҠЁзұ»еҠ е…Ҙfeignзӣёе…іжіЁйҮҠпјҡ
@SpringBootApplication @ComponentScan(basePackages = {"com.distribute"}) @EnableFeignClients(basePackages = "com.distribute") //еӣ дёәfeignжҺҘеҸЈе®ҡд№үзҡ„еҢ…дёҺйЎ№зӣ®дёҚеҗҢзә§ йЎ№зӣ®й»ҳи®Өжү«жҸҸcom.distribute.gateway public class GatewayApplication { public static void main(String[] args) { SpringApplication.run(GatewayApplication.class, args); } }
жӯӨж—¶еҗҜеҠЁgatewayйҖҡиҝҮfeignи°ғз”Ёadmin-userйЎ№зӣ®дёӯзҡ„ж–№жі•дҫқ然иҝҳжҳҜжҠҘй”ҷпјҢйңҖиҰҒеўһеҠ еҰӮдёӢй…ҚзҪ®зұ»пјҡ
/** *@Description <жүӢеҠЁжіЁе…ҘBean Spring Cloud GatewayжҳҜеҹәдәҺWebFluxзҡ„пјҢжҳҜReactiveWebпјҢжүҖд»ҘHttpMessageConvertersдёҚдјҡиҮӘеҠЁжіЁе…ҘгҖӮеҰӮжһңдёҚжіЁе…ҘпјҢspringcloudGatewayи°ғз”Ёfeignж—¶дјҡжҠҘй”ҷ * No qualifying bean of type 'org.springframework.boot.autoconfigure.http.HttpMessageConverters> */ @Configuration public class FeignConfig { @Bean @ConditionalOnMissingBean public HttpMessageConverters messageConverters(ObjectProvider<HttpMessageConverter<?>> converters) { return new HttpMessageConverters(converters.orderedStream().collect(Collectors.toList())); } }
еҗҺиҮӘиЎҢи®ҫзҪ®ејӮеёёдҝЎжҒҜпјҡ
жІЎжңүжқғйҷҗпјҡ
{ "code": 401, "data": "", "message": "жІЎжңүиў«жҺҲжқғжҲ–иҖ…жҺҲжқғе·Із»ҸеӨұж•Ҳ", "success": false }
йүҙжқғжҲҗеҠҹпјҡ
{ "data": [ "з®ЎзҗҶе‘ҳ" ], "success": true, "code": 200, "message": "иҜ·жұӮе·Із»ҸжҲҗеҠҹеӨ„зҗҶ" }
jwtе·Ҙе…·зұ»пјҡ
@Component public class JwtUtil { //еҠ еҜҶ и§ЈеҜҶж—¶зҡ„еҜҶй’Ҙ з”ЁжқҘз”ҹжҲҗkey public static final String JWT_KEY = "IT1995"; /** * з”ҹжҲҗеҠ еҜҶеҗҺзҡ„з§ҳй’Ҙ secretKey * @return */ public static SecretKey generalKey() { byte[] encodedKey = Base64.getDecoder().decode(JwtUtil.JWT_KEY); SecretKey key = new SecretKeySpec(encodedKey, 0, encodedKey.length, "AES"); return key; } public static String createJWT(String id, String subject, long ttlMillis){ SignatureAlgorithm signatureAlgorithm = SignatureAlgorithm.HS256; //жҢҮе®ҡзӯҫеҗҚзҡ„ж—¶еҖҷдҪҝз”Ёзҡ„зӯҫеҗҚз®—жі•пјҢд№ҹе°ұжҳҜheaderйӮЈйғЁеҲҶпјҢjwtе·Із»Ҹе°ҶиҝҷйғЁеҲҶеҶ…е®№е°ҒиЈ…еҘҪдәҶгҖӮ long nowMillis = System.currentTimeMillis();//з”ҹжҲҗJWTзҡ„ж—¶й—ҙ Date now = new Date(nowMillis); SecretKey key = generalKey();//з”ҹжҲҗзӯҫеҗҚзҡ„ж—¶еҖҷдҪҝз”Ёзҡ„з§ҳй’Ҙsecret,иҝҷдёӘж–№жі•жң¬ең°е°ҒиЈ…дәҶзҡ„пјҢдёҖиҲ¬еҸҜд»Ҙд»Һжң¬ең°й…ҚзҪ®ж–Ү件дёӯиҜ»еҸ–пјҢеҲҮи®°иҝҷдёӘз§ҳй’ҘдёҚиғҪеӨ–йңІе“ҰгҖӮе®ғе°ұжҳҜдҪ жңҚеҠЎз«Ҝзҡ„з§Ғй’ҘпјҢеңЁд»»дҪ•еңәжҷҜйғҪдёҚеә”иҜҘжөҒйңІеҮәеҺ»гҖӮдёҖж—Ұе®ўжҲ·з«Ҝеҫ—зҹҘиҝҷдёӘsecret, йӮЈе°ұж„Ҹе‘ізқҖе®ўжҲ·з«ҜжҳҜеҸҜд»ҘиҮӘжҲ‘зӯҫеҸ‘jwtдәҶгҖӮ JwtBuilder builder = Jwts.builder() //иҝҷйҮҢе…¶е®һе°ұжҳҜnewдёҖдёӘJwtBuilderпјҢи®ҫзҪ®jwtзҡ„body // .setClaims(claims) //еҰӮжһңжңүз§ҒжңүеЈ°жҳҺпјҢдёҖе®ҡиҰҒе…Ҳи®ҫзҪ®иҝҷдёӘиҮӘе·ұеҲӣе»әзҡ„з§Ғжңүзҡ„еЈ°жҳҺпјҢиҝҷдёӘжҳҜз»ҷbuilderзҡ„claimиөӢеҖјпјҢдёҖж—ҰеҶҷеңЁж ҮеҮҶзҡ„еЈ°жҳҺиөӢеҖјд№ӢеҗҺпјҢе°ұжҳҜиҰҶзӣ–дәҶйӮЈдәӣж ҮеҮҶзҡ„еЈ°жҳҺзҡ„ .setId(id) //и®ҫзҪ®jti(JWT ID)пјҡжҳҜJWTзҡ„ж ҮиҜҶпјҢж №жҚ®дёҡеҠЎйңҖиҰҒпјҢиҝҷдёӘеҸҜд»Ҙи®ҫзҪ®дёәдёҖдёӘдёҚйҮҚеӨҚзҡ„еҖјпјҢдё»иҰҒз”ЁжқҘдҪңдёәдёҖж¬ЎжҖ§token,д»ҺиҖҢеӣһйҒҝйҮҚж”ҫж”»еҮ»гҖӮ .setIssuedAt(now) //iat: jwtзҡ„зӯҫеҸ‘ж—¶й—ҙ .setSubject(subject) //sub(Subject)пјҡд»ЈиЎЁиҝҷдёӘJWTзҡ„дё»дҪ“пјҢеҚіе®ғзҡ„жүҖжңүдәәпјҢиҝҷдёӘжҳҜдёҖдёӘjsonж јејҸзҡ„еӯ—з¬ҰдёІпјҢеҸҜд»Ҙеӯҳж”ҫд»Җд№ҲuseridпјҢroldidд№Ӣзұ»зҡ„пјҢдҪңдёәд»Җд№Ҳз”ЁжҲ·зҡ„ж Үеҝ—гҖӮ .signWith(signatureAlgorithm, key);//и®ҫзҪ®зӯҫеҗҚдҪҝз”Ёзҡ„зӯҫеҗҚз®—жі•е’ҢзӯҫеҗҚдҪҝз”Ёзҡ„з§ҳй’Ҙ if (ttlMillis >= 0) { long expMillis = nowMillis + ttlMillis; Date exp = new Date(expMillis); builder.setExpiration(exp); //и®ҫзҪ®иҝҮжңҹж—¶й—ҙ } return builder.compact(); //е°ұејҖе§ӢеҺӢзј©дёәxxxxxxxxxxxxxx.xxxxxxxxxxxxxxx.xxxxxxxxxxxxxиҝҷж ·зҡ„jwt } public static Claims parseJWT(String jwt){ SecretKey key = generalKey(); //зӯҫеҗҚз§ҳй’ҘпјҢе’Ңз”ҹжҲҗзҡ„зӯҫеҗҚзҡ„з§ҳй’ҘдёҖжЁЎдёҖж · Claims claims = Jwts.parser() //еҫ—еҲ°DefaultJwtParser .setSigningKey(key) //и®ҫзҪ®зӯҫеҗҚзҡ„з§ҳй’Ҙ .parseClaimsJws(jwt).getBody();//и®ҫзҪ®йңҖиҰҒи§Јжһҗзҡ„jwt return claims; } public static void main(String[] args){ Account account = new Account(); account.setUserName("it1995"); account.setPassword("123456"); String jwt = createJWT(UUID.randomUUID().toString(), JSONUtil.toJsonStr(account), 3600 * 24); System.out.println("еҠ еҜҶеҗҺпјҡ" + jwt); //и§ЈеҜҶ Claims claims = parseJWT(jwt); System.out.println("и§ЈеҜҶеҗҺпјҡ" + claims.getSubject()); } }
з»ҹдёҖз»“жһңиҝ”еӣһзұ»пјҡ
package com.distribute.common; import lombok.AllArgsConstructor; import lombok.Data; /** * @author пјҡfengwenzhe * @date пјҡCreated in 2023/2/2 20:38 * ж–Ү件иҜҙжҳҺпјҡ </p> */ @Data @AllArgsConstructor public class CommonResult { private Object data; private boolean success; private Integer code; private String message; //з§ҒжңүеҢ–пјҢйҳІжӯўnew private CommonResult() {} //жҲҗеҠҹ public static CommonResult ok(Object data, HttpStatusCode statusCode) { return new CommonResult(data,true,statusCode.code,statusCode.zhMessage); //code д№ҹеҸҜд»ҘдҪҝз”Ёеӯ—е…ёз®ЎзҗҶ } //жҲҗеҠҹиҝ”еӣһ йҮҚиҪҪ messageжІЎжңүзү№еҲ«иҰҒжұӮ public static CommonResult ok(Object data) { return CommonResult.ok(data, HttpStatusCode.OK); //message д№ҹеҸҜд»ҘдҪҝз”Ёеӯ—е…ёз®ЎзҗҶ } // еӨұиҙҘ public static CommonResult error( HttpStatusCode statusCode) { return new CommonResult("",false, statusCode.code, statusCode.zhMessage); } }
package com.distribute.common; import lombok.Data; public enum HttpStatusCode { /** * httpзҠ¶жҖҒз ҒжһҡдёҫжүҖжңүзҠ¶жҖҒз ҒжіЁи§Ј */ USERNAME_PASSWORD_DENY(1000, "username password deny", "з”ЁжҲ·еҗҚжҲ–еҜҶз Ғй”ҷиҜҜ"), OK(200, "OK", "иҜ·жұӮе·Із»ҸжҲҗеҠҹеӨ„зҗҶ"), OPERATION_TYPE_ERROR(512, "", "ж“ҚдҪңзұ»еһӢдёҚжӯЈзЎ®"); //й”ҷиҜҜз Ғ public Integer code; //жҸҗзӨәдҝЎжҒҜ public String enMessage; //жҸҗзӨәдҝЎжҒҜ public String zhMessage; HttpStatusCode(int code, String enMessage, String zhMessage) { this.code = code; this.enMessage = enMessage; this.zhMessage = zhMessage; } }
